In digital security, mastering the fundamentals is non-negotiable. Two of the most critical—and frequently confused—concepts are authentication and authorization. Understanding the difference is not just a technicality; it's the foundation of any secure and scalable system.
Simply put, authentication confirms who you are, while authorization determines what you’re allowed to do. Confusing them is a direct path to severe security vulnerabilities, data breaches, and a loss of customer trust.
Authentication vs. Authorization: A Practical Guide
Every secure system is built on controlling access. To do this effectively, you must master the distinction between these two concepts. They work in tandem, but they are not interchangeable. Getting this right is the cornerstone of any trustworthy application, from a global fintech platform to an enterprise SaaS product.
Let’s use a real-world analogy: entering a secure office building.
- Authentication is showing your photo ID at the reception desk. The guard verifies your face against the ID to confirm you are who you claim to be. This is a one-time identity verification step.
- Authorization is the keycard you receive after your identity is confirmed. This card is programmed with specific permissions. It will unlock your team's floor and the cafeteria but won't grant access to the server room or the CEO's office.
Authentication always comes first. A system cannot grant permissions (authorize) until it has definitively verified the user's identity (authenticated).
The Business Impact of Getting It Wrong
When a system authenticates a user but fails to properly check their authorization, the consequences are immediate and severe. Imagine a junior employee accessing sensitive financial reports or a customer inadvertently gaining access to another user's private data.
These failures lead directly to data breaches, steep regulatory fines (like GDPR and CCPA), and an irreversible loss of customer trust. For businesses in SaaS, finance, and e-commerce, this isn't an abstract risk—it's a direct threat to revenue and reputation. Modern verification technologies can lock this down, and it's worth exploring the different biometric authentication methods that are becoming the new standard for user security.
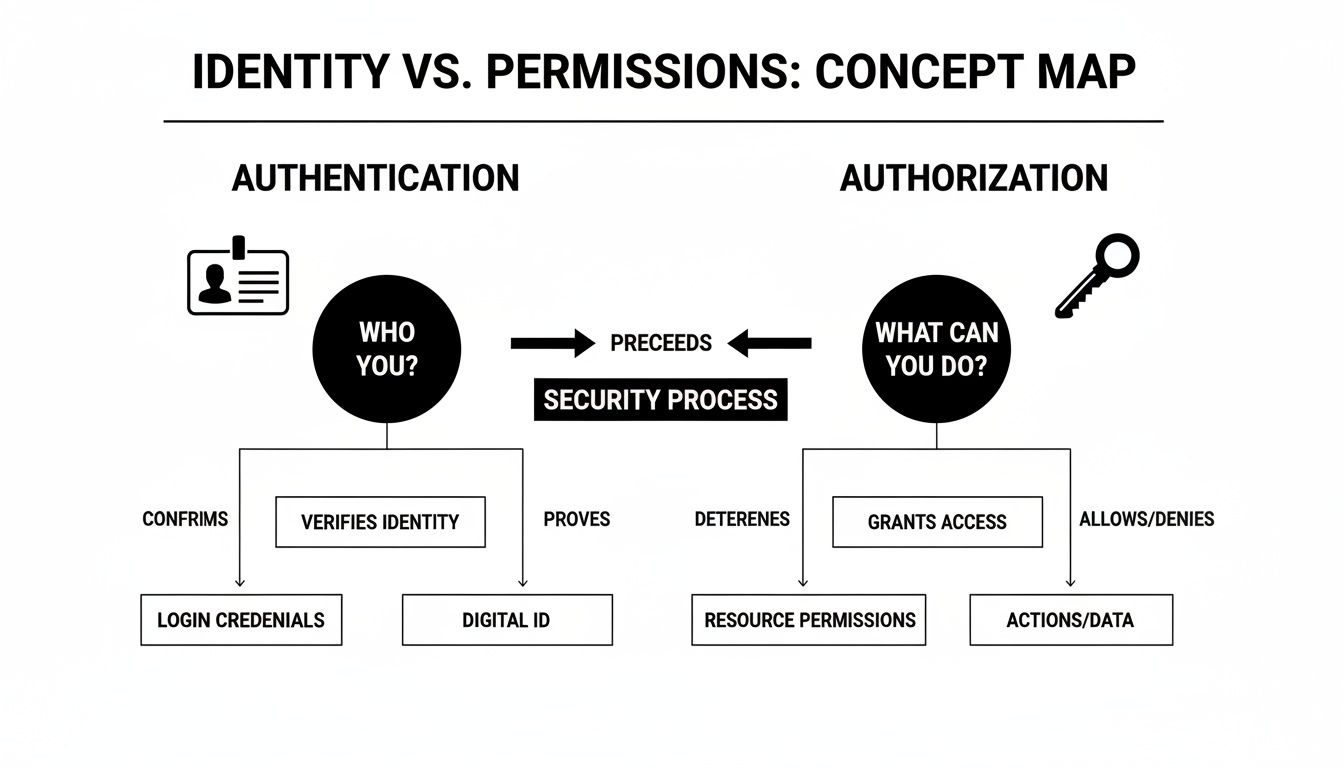
This diagram helps visualize how these two distinct steps form a complete security process.
The image clearly shows identity verification as the first gate, with permission granting following as a separate, critical action.
Authentication vs Authorization At a Glance
For a quick reference, this table breaks down the core differences between the two concepts.
| Aspect | Authentication (Proving Your Identity) | Authorization (Defining Your Permissions) |
|---|---|---|
| Purpose | To verify a user's identity and confirm they are who they say they are. | To grant or deny specific permissions to an authenticated user. |
| Question | "Who are you?" | "What are you allowed to do?" |
| Process | User provides credentials (password, token, biometric scan). | System checks access control policies against the user's identity. |
| Output | A secure token or session confirming identity. | An access decision (allow/deny) for a specific resource or action. |
| Analogy | Showing your ID at an event. | Your ticket type (GA, VIP, backstage). |
This direct comparison makes it clear how authentication is the key, and authorization is deciding which doors that key can open.
Authorization is where the "Principle of Least Privilege" is enforced. Once a user's identity is confirmed, the system must only grant the absolute minimum access needed for them to do their job—and nothing more.
This principle is put into practice with structured permission models. A great example is Role Based Access Control (RBAC), which simplifies security management by assigning permissions to roles (like "admin" or "editor") instead of to individuals.
Why Secure Identity Is Your Biggest Business Imperative
Let's move past the technical jargon and focus on what this means for your business. In today's digital economy, weak identity security isn't just an IT problem—it's a direct threat to your revenue, reputation, and operational stability. Getting this wrong leads to immediate and expensive consequences.
For any modern company, especially in sectors like finance, government, or SaaS, strong identity practices are non-negotiable. This extends to foundational identity verification processes like KYC and KYB, which ensure you’re dealing with legitimate customers and partners. Cutting corners here is an open invitation to fraud and regulatory penalties.
The True Cost of Inadequate Security
Weak identity controls are the front door for data breaches. The financial fallout from a single incident can be devastating, extending far beyond immediate cleanup costs to include lasting brand damage and a total loss of customer trust.
A robust authentication and authorization framework is your first and best line of defense. It shifts security from a reactive, damage-control function into a proactive asset that protects your value.
This proactive stance is essential for meeting compliance mandates like GDPR, CCPA, and HIPAA, where fines for mishandling data can run into the millions. For our SaaS and fintech clients, this isn't an abstract risk; it’s a daily operational reality that shapes how products are designed from day one.
Gaining a Competitive Advantage
Conversely, a strategic investment in identity management creates a powerful competitive edge. When customers trust that their data is secure, they become loyal advocates for your brand. This trust is the foundation for scaling your business, whether you're a startup gaining market traction or an enterprise expanding into new territories.
Actionable Security as a Business Driver
If you're building a product, embedding strong security like Multi-Factor Authentication (MFA) early in the development cycle is simply smart business. It is far more efficient and cost-effective to build security in from the start than to bolt it on after a breach.
Here’s how prioritizing secure identity drives business forward:
- Protecting Revenue and Reputation: Secure systems prevent the breaches that erode customer trust and impact your bottom line.
- Enabling Compliance: Strong controls are a prerequisite for meeting data protection laws, helping you avoid massive fines.
- Fostering Customer Loyalty: A secure and transparent user experience builds confidence, a key differentiator in any crowded market.
- Driving Scalable Growth: A solid security foundation allows you to grow your user base and expand confidently without introducing unacceptable risk.
For our clients, whether an agile startup or a large enterprise, the principle is the same. Strong authentication and authorization aren't just features—they are the fundamental pillars of any resilient and successful digital business.
Decoding the Protocols That Power Modern Security
If you're building any kind of application today, you're also in the business of managing security. Behind every secure login and permission granted is a set of core technologies. These protocols are the engines driving modern identity and access control, and knowing which one to use—and why—is a critical architectural decision.
Let's walk through the essential protocols your team will encounter, using clear analogies to explain what they do and where they fit in your technology stack.
OAuth 2.0: The Valet Key for Your Data
Think of OAuth 2.0 as a digital "valet key." You can give a valet a key that lets them park your car, but it won't open the trunk or glove compartment. OAuth 2.0 does the same thing for user data.
It’s an authorization framework. It gives a third-party app limited access to a user's data on another service without the user ever handing over their password. When a photo printing service asks to access your Google Photos, that’s OAuth 2.0 at work. You grant permission for that specific task, but the app never sees your Google password.
OAuth 2.0 is purely about granting access, not proving identity. It answers the question, "What can this app do on my behalf?" It never answers, "Who is this user?" That crucial distinction brings us to our next protocol.
OpenID Connect (OIDC): The ID Check on Top
If OAuth 2.0 is the valet key, then OpenID Connect (OIDC) is the driver's license the valet checks before taking your keys. OIDC is a lean identity layer built directly on top of OAuth 2.0, adding the missing authentication piece to the flow.
Anytime you see a "Sign in with Google" or "Login with Facebook" button, you're looking at OIDC. It follows the standard OAuth 2.0 process but adds one vital component: an ID Token. This token, usually a JWT, contains verifiable claims about who you are—your name, email, and a unique user ID.
- OAuth 2.0 provides an Access Token, which grants permissions.
- OIDC provides an ID Token to prove identity plus an Access Token to grant permissions.
This powerful combination lets an application verify who you are and request specific access rights all in one streamlined flow.
SAML: The Corporate Single Sign-On Standard
Security Assertion Markup Language (SAML) is the seasoned veteran of federated identity, especially within the enterprise world. Imagine it as a corporate security badge that gets you into every building on campus. You swipe it once at the main gate, and then you have access to the office, the cafeteria, and the lab without having to badge in at every single door.
SAML is the workhorse behind most corporate Single Sign-On (SSO) systems. An Identity Provider (IdP), like Microsoft Active Directory, authenticates a user once. It then sends a digitally signed SAML "assertion" to each application (the Service Provider). This assertion is a trusted message that tells the app, "This user is authenticated, and here's what they're allowed to do."
JWT: The Digital Passport for Permissions
JSON Web Tokens (JWTs) aren't a protocol like OAuth or SAML. Instead, a JWT is a compact, self-contained standard for securely transmitting information as a JSON object. The best analogy is a digital passport. It contains verified information (claims) about your identity and permissions, all digitally signed so it can be trusted without question.
JWTs are ubiquitous in modern web and mobile apps, forming the backbone of API security. After a user logs in, the server generates a JWT and sends it to the client. The client then includes this token in the header of every API call, proving its right to access protected resources without forcing the server to look up permissions in a database every single time. To go deeper on protecting your endpoints, our guide on REST API security best practices offers practical strategies.
With the right protocols in your toolkit, it’s time to start architecting. The decisions you make at this stage will define your system’s security, scalability, and user experience. One of the most critical forks in the road is choosing between stateful and stateless architecture. This choice has major ripple effects on everything from your DevOps workflow to your company's growth potential.
The traditional approach is a stateful, session-based system. When a user logs in, the server creates a session record and gives the client a session ID, usually in a cookie. On every subsequent request, the server must look up that session to determine who the user is and what they’re allowed to do.
This works for simple, monolithic apps. But in a modern, distributed environment, it quickly becomes a bottleneck. If you're running multiple servers, you suddenly need a shared session store (like Redis) so any server can handle the request. This adds a new layer of complexity and another potential point of failure.
The Power of Stateless, Token-Based Systems
This is where stateless, token-based architectures—usually built on JWTs—really shine. After a user authenticates, the server generates a self-contained JWT that holds the user’s identity and permissions. It’s digitally signed and sent to the client, which then includes this token with every API request.
Because the token contains all the necessary information and can be verified by its signature, the server doesn't need to remember anything. Any server can validate the token independently, a perfect fit for microservices, cloud-native apps, and any load-balanced setup.
This stateless model is the foundation for building scalable, resilient systems. By eliminating server-side session management, you simplify your backend, reduce database load, and create a more flexible architecture that's easier to maintain and scale.
Blueprints for Different Platforms
How you implement authentication and authorization will differ slightly across platforms. Here's a breakdown of the patterns we use when building secure backends for SaaS products and enterprise clients.
Securing Web Applications
For modern Single-Page Applications (SPAs), the standard is to store JWTs in memory and attach them to API calls. If you decide to manage tokens with cookies, you absolutely must lock them down.
- HttpOnly Flag: This is your first line of defense. It prevents JavaScript from accessing the cookie, which helps shut down cross-site scripting (XSS) attacks.
- Secure Flag: Simple but effective. It ensures the cookie is only ever sent over an HTTPS connection.
- SameSite Attribute: This controls when a browser sends the cookie with cross-origin requests, protecting you from Cross-Site Request Forgery (CSRF). Setting it to
StrictorLaxis non-negotiable.
Securing Mobile Applications
On mobile, security is about protecting tokens on the device itself. Storing a sensitive token in plaintext local storage is a massive vulnerability. We cover this in-depth in our guide on mobile app security best practices.
The only correct way to do it is with the platform’s built-in secure storage.
- iOS: Use Keychain Services. It’s an encrypted database designed specifically for storing secrets like tokens.
- Android: Use EncryptedSharedPreferences or the Android Keystore system. They provide the same kind of secure, hardware-backed storage.
Securing APIs
For APIs, especially in a microservices architecture, every single request must be treated as if it’s coming from an untrusted source. This means every request must be authenticated and authorized independently. Token validation and scope-based controls are your essential tools.
When an API gateway or an individual service gets a request, it should run these checks:
- Validate the JWT Signature: First, confirm the token is legitimate and hasn't been tampered with.
- Check Expiration: Next, reject any token that has expired. No exceptions.
- Verify Scopes: Finally, check the
scopeclaim inside the token. This confirms the user (or client app) is actually authorized to perform the requested action, likeread:invoicesversuswrite:invoices.
This process rigorously enforces the Principle of Least Privilege at the API level. It ensures services can only do what they are explicitly permitted to do—a fundamental practice for building a trustworthy system.
Your Checklist for Real-World Security
Moving from sound architecture to implementation is where the real work begins. This requires a disciplined set of security habits your team should treat as non-negotiable. A solid authentication and authorization strategy isn't just about picking the right protocols; it's about applying best practices consistently.
Ignoring these fundamentals is like building a bank vault with a screen door. This checklist will help you turn abstract security concepts into a concrete action plan, making your system resilient by design, not by chance.
Enforce Multi-Factor Authentication Everywhere
If you do only one thing from this list, make it this one. Multi-Factor Authentication (MFA) is the single most powerful step you can take to protect user accounts. By requiring two or more verification methods, you build a layered defense that makes stolen passwords practically useless.
Why it matters: Passwords are your weakest link. Cyber breaches cost the world a staggering USD 8 trillion in 2023 alone, and with 82% of those breaches involving weak or stolen credentials, MFA is no longer an optional feature—it's the baseline. You can discover insights on the advanced authentication market to see where this trend is heading.
How to get it right:
- Make MFA mandatory for everyone, especially accounts with admin privileges.
- Give users choices for their second factor, like authenticator apps (TOTP), hardware keys (FIDO2/WebAuthn), or biometrics.
- Integrate MFA checks at every critical point: login, password resets, and any change to sensitive account details.
Stick to the Principle of Least Privilege
The Principle of Least Privilege (PoLP) is a foundational security concept: a user should only have the absolute minimum permissions needed to perform their job. Nothing more.
Why it matters: Over-provisioning access creates a massive attack surface. If a privileged account gets compromised, PoLP drastically limits the damage. In a fintech app, this means a customer service agent can look up a transaction history but has no ability to initiate a money transfer.
Start by denying all access by default. Only grant specific, granular permissions based on a clearly defined role and a real business need. This fundamentally shifts your security posture from "trust but verify" to "never trust, always verify."
How to get it right:
- Use Role-Based Access Control (RBAC) to manage permissions by assigning them to roles, not individuals.
- Schedule regular audits of user permissions and promptly remove any access that's no longer necessary.
- For an e-commerce platform, a "shipping manager" role should be able to process orders but never see a customer's full payment details.
Master Secure Token Management
Think of tokens, like JWTs, as the keys to your digital kingdom. How you manage their entire lifecycle—from creation to revocation—is absolutely critical. Getting this wrong is a fast track to a major breach.
Why it matters: A stolen token with a long expiration date gives an attacker a persistent key to your APIs and user data. Smart token management ensures that even if a token is compromised, the window of opportunity for an attacker is incredibly small.
Here are the non-negotiables for handling tokens:
- Secure Storage: Never store tokens in
localStorage. Use secure,HttpOnlycookies for web apps. For mobile, use the device's built-in secure storage: Keychain for iOS and Keystore for Android. - Short Lifespans: Keep your access tokens on a very short leash—think 5-15 minutes. Use long-lived refresh tokens to get new access tokens in the background without forcing the user to constantly log in again.
- Robust Revocation: You need a bulletproof way to invalidate tokens instantly. This is essential when a user logs out, changes their password, or you suspect a compromise. A token denylist or blocklist is a common and effective pattern here.
Maintain Comprehensive Audit Trails
You can't secure what you can't see. Detailed logging and audit trails provide a clear, immutable record of who did what, where, and when. This is your best friend for both incident response and meeting compliance standards.
Why it matters: When a security incident happens, your logs are the first place you'll turn to understand the what, when, and how. In regulated industries like finance and healthcare, detailed audit trails aren't just a good idea—they're a legal requirement.
How to get it right:
- Log all critical authentication and authorization events: successful logins, failed attempts, password changes, permission updates, and token refreshes.
- Ensure every log entry includes key context: user ID, IP address, a precise timestamp, and the specific action taken.
- Use a centralized logging solution to aggregate this data, making it easy to monitor and set up alerts for suspicious activity in real time.
Choosing Your Path: Startup vs. Enterprise Security
There's no single playbook for security. When it comes to authentication and authorization, the path for a lean startup building its first product looks entirely different from that of a global enterprise with a sprawling digital footprint. Your resources, regulatory duties, and existing tech all shape the right approach for you.
For a startup, everything is about speed and smart spending. The mission is to launch a secure product fast, without tying up your best engineers building an identity system from the ground up. This is where managed identity platforms, or Identity as a Service (IDaaS), become a game-changer.
Enterprises, however, are playing a different game. Their world revolves around making new applications fit into massive, pre-existing identity systems like Microsoft Active Directory. They have to navigate complex compliance rules and maintain tight governance over every digital asset.
The Startup Playbook: Rapid and Secure Launch
If you're a startup, your smartest move is to lean on managed services like Auth0, Okta, or AWS Cognito. These platforms handle the heavy lifting of security, providing battle-tested solutions right out of the box.
- User Registration and Login: Get secure, pre-built sign-up and login flows ready to go.
- Social Logins: Easily integrate popular options like Google, Facebook, and Apple.
- Multi-Factor Authentication (MFA): Add this critical security layer with just a few clicks.
- Compliance: Gain built-in support for crucial standards like OpenID Connect and SAML.
By offloading identity management, your team stays focused on what they do best: building your core product. This accelerates your time to market and ensures your MVP is built on a proven, secure foundation without a huge upfront investment.
The identity verification and authentication market is booming, especially with cloud-based tools that are essential for remote teams. Startups scaling with offshore engineers can use these services to create zero-trust environments, potentially saving up to 60% on costs while building strong cybersecurity from day one.
The Enterprise Blueprint: Integration and Governance
For large organizations, security is all about integration and fine-tuned control. The main priority is making sure new services work perfectly with what you already have. This often means building custom Identity and Access Management (IAM) platforms or expanding existing ones.
Here’s what enterprises must consider:
- Federation with Existing Systems: Connecting with corporate directories (like Active Directory) using protocols like SAML or OIDC to enable Single Sign-On (SSO).
- Complex Compliance: Meeting strict industry regulations (like HIPAA or PCI-DSS) that require granular control and meticulous audit trails.
- Bespoke Authorization Logic: Creating custom permission models that mirror complex internal business rules and organizational charts.
- Scalability and Performance: Architecting systems that can support millions of users and transactions without compromising on speed or security.
At Group107, our dedicated teams are fluent in both worlds. We help startups integrate managed identity services to launch securely and quickly. For enterprises, we partner to co-develop custom IAM solutions, offering full IP transparency and ensuring the final system fits perfectly with your existing infrastructure and long-term vision.
Common Questions About Authentication and Authorization
Once you move past the theory, you’ll start hitting practical questions. Building a secure system means making tough choices on protocols and architecture. Here are some straightforward answers to the common hurdles teams face when setting up authentication and authorization.
What Is the Real Difference Between OAuth2 and OIDC?
This one trips up a lot of people, but it’s simpler than it sounds. Think of it this way: OAuth 2.0 is for authorization—it grants permission. OpenID Connect (OIDC) is for authentication—it confirms who someone is.
For instance, OAuth 2.0 lets an app access your Google Photos for you, but it never actually tells the app your name or email. It just provides a token to get the photos.
OIDC is a thin layer built right on top of OAuth 2.0 to solve that exact problem. It adds a standardized ID Token (which is a JWT) that contains verifiable user info. So, OAuth 2.0 gets the "key" to the data, and OIDC tells the app whose "key" it is.
When Should I Use Stateless JWTs Versus Stateful Sessions?
Your choice here really comes down to your system’s architecture. Each approach has clear wins depending on what you’re building.
Choose stateless JWTs for modern, distributed systems. If you're working with microservices, mobile apps, or Single Page Applications (SPAs), JWTs are your best bet. They are self-contained, meaning they carry all the user info needed, which makes them incredibly scalable. Your servers don’t need to remember a thing.
Choose stateful sessions for more traditional, monolithic web apps. Sessions are often easier to implement on a single server and make it dead simple to invalidate a user's session instantly (like on logout). Doing the same with JWTs requires more complex workarounds.
Is Multi-Factor Authentication Really a Must-Have for My App?
Yes. Absolutely. In today's world, relying on just a password is a massive liability. Stolen credentials are the number one cause of data breaches, which makes single-factor authentication a dangerously weak link.
MFA is the single most effective security control you can implement, proven to block over 99% of automated attacks. For any app that touches sensitive user data, financial details, or PII, MFA isn’t just a nice-to-have feature. It’s a baseline requirement to protect your users—and your business—from serious reputational and financial harm.
Putting a strong authentication and authorization framework in place is fundamental to building a product that lasts. It safeguards your assets, builds trust with your customers, and sets a solid foundation for growth.
Summary and Next Steps
Mastering authentication and authorization is not just an IT task; it's a strategic business imperative. By understanding the core differences, choosing the right protocols like OAuth 2.0 and OIDC, and implementing best practices like MFA and the Principle of Least Privilege, you can build a secure, scalable, and trustworthy platform.
Your next steps should be:
- Review your current system: Identify whether you are correctly separating authentication from authorization.
- Assess your MFA implementation: If it's not mandatory for all users, especially admins, make it a priority.
- Audit user permissions: Enforce the Principle of Least Privilege by revoking unnecessary access rights.
- Evaluate your token management strategy: Ensure tokens have short lifespans and are stored securely.
Ready to build a secure, scalable platform with a team of expert engineers? At Group107, we deliver dedicated offshore software development teams that integrate seamlessly with your organization, helping you accelerate development while maintaining the highest security standards. Discover how we can turn your vision into a secure, market-ready reality by visiting https://group107.com.